You don’t have to be a Snowden to know how to blog securely: a simple guide
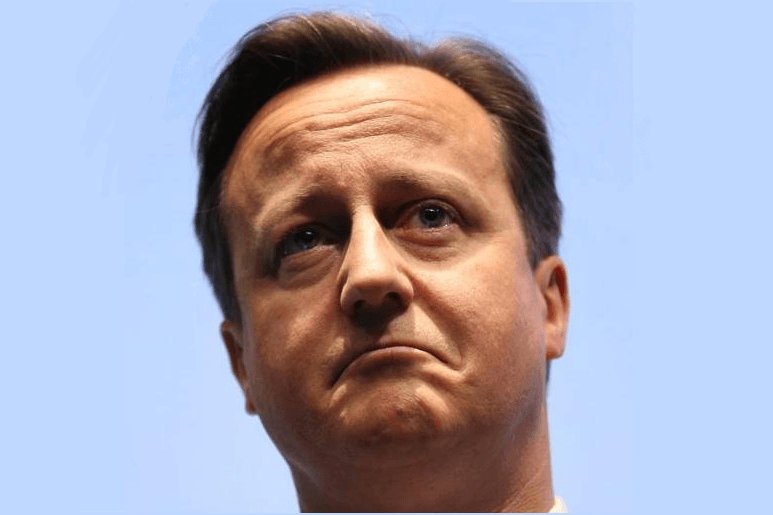
With the recent revelation that Yahoo passed millions of its user accounts to the US National Security Agency (a partner with GCHQ, the UK equivalent) and with the new “Snoopers Charter” legislation going through the British parliament, it’s not surprising that many Internet users – bloggers, political activists – may want to find out, in simple terms, how to be safe online from predators (‘Big Brother’, consumer organisations and those who simply wish to steal identities). Well, here’s one way…
For simplicity, this guide outlines one route: via The Amnesic Incognito Live System (Tails). The guide only deals with internet connections, operating systems, browsers and email. The advice given is not meant to be exhaustive. Discipline is essential and additional security tips are provided in the last section.
Internet connection
Purchase in cash a pay-as-you-go 4G mobile broadband device. Top it up, again in cash, via different convenience stores. Use this connection for all your blogging (writing, research etc). Avoid other ways of connecting.
[Quick note for whistleblowers…If you merely wish to transmit files, do this: 1. Make sure nothing on your computer files identifies you. 2. Download and install Tor bundle (see below) to a USB stick. 3. At an Internet cafe transmit files via Tor (preferably to an outlet using SecureDrop.]
Tails
Ideally you should be using an open source operating system, as these tend to be more secure. Tails is one such system and includes a range of security applications. The easiest way to get Tails is to purchase, for around £10, a pre-loaded USB stick from E-bay or Amazon, or any other online retailer that sells this product.
Once you have one, switch on your Internet connection, insert the Tails USB stick into a USB socket, boot up the PC and press the F12 key to get Boot options – choose boot from USB, then on the next screen click Tails Live. (Note that Tails can be slow loading the Tails desktop.)
The first time you access Tails you’ll be asked if you want Persistence (whereby you store your files on Tails). If you click yes, you’ll be asked to choose a password. (Note: if you forget this password you’ll not be able to use Persistence again.)
Next you are asked if you want more options. If you click yes, you can choose to mask your PC’s MAC address (the unique number that identifies your machine). Note: if you choose this, your Internet experience may be slow. You are also asked if you want this option every time you boot up Tails.
Once the Tails desktop is up you can explore Tails at will (it includes an open-source Office suite).
Using Tor
To start the Internet via Tails you need to click on the little arrow at the top-right of the desktop, then click on Wi-fi, then Wi-fi settings. From there click on your Wi-fi device (and input the password for it). Close the Network settings window.
It can take a minute or two before a message pops up saying that the Tor browser – which comes with Tails as the default browser – is ready.
Tor is a highly customised version of the Firefox browser and comes with a number of built-in security features, such as HTTPS Everywhere and NoScript. Tor provides you with a different IP address every time you use it, so making your browsing ‘anonymous’ (see also ‘Enhanced security tips’ section below).
To start Tor, click on Applications, then Tor.
Here’s Edward Snowden’s advice on online security including, for example, Tor:
I think Tor is the most important privacy-enhancing technology project being used today. I use Tor personally all the time. We know it works from at least one anecdotal case that’s fairly familiar to most people at this point. That’s not to say that Tor is bulletproof. What Tor does is it provides a measure of security and allows you to disassociate your physical location.
Encrypted email
Tails also comes with Icedove, an enhanced security version of the Thunderbird email client that automatically encrypts your outgoing mail (unless you instruct otherwise). You can use it to access trusted cloud-based email accounts.
Examples of reasonably secure cloud-based email accounts are ProtonMail and Riseup (you need two recommendations from existing Riseup users to get an account).
End-to-end encryption only applies if both email users are using the same service that offers such a facility. But for added security you may also wish to use PGP (Pretty Good Privacy). Fortunately, Tails can organise this for you via Enigmail (an add-on to Icedove). To see how to use Icedove and organise PGP (via Tails) click here.
Once you have your PGP private and public keys set up, you can send and receive encrypted files (messages) via your email provider, using Icedove/Enigmail. But to translate encrypted files received you will need to use a handy online tool – here’s one.
Hide your metadata
Metadata is hidden on every document you produce (text, images, pdfs etc.) and provides basic information on author, data created, etc. Tails can’t automatically clear the metadata from your files, but it does provide a tool – MAT (Metadata Anonymisation Toolkit) – that can.
For more info on Tails and what it can do (and can’t) click here.
Meanwhile, here’s some advice from the experts – video below…
https://youtu.be/aviUKt7adU8
Enhanced security tips
- Use a dedicated PC and Internet connection for blogging/research. Do not use any other device for this activity. Ensure you never reveal your real identity when using this PC (e.g. via email usage or online registration).
- If you prefer an operating system other than Tails, you may want to consider installing on to your PC (if need be in a separate partition) other Linux-based systems, such as Ubuntu or Mint (and customise the tools therein).
- If you need to provide a phone number to access certain online services – e.g. a proxy email – use a pay-as-you-go sim card (and top it up as needed) on your burner mobile.
- Needless to say, do not use Skype or an equivalent with your online blogging device.
- You may want to use a VPN (though this is not essential if using Tails).
- If you’re concerned about viruses and malware, consider using the DVD version of Tails.
- Avoid talking to friends, associates, etc. about your blogging.
- Configure all devices and applications (e.g. Tor) to avoid tracking.
- For added security you may also want to encrypt your PC (even if only using it to boot up Tails).
- Cover up any built-in cameras on your blogging device; mute the audio.
- Be careful what you reveal about your blogging identity on social media; consider posting disinformation.
Good luck!
Get Involved!
– Read up on the latest from Big Brother Watch
– Donate to the Electronic Frontier Foundation
– Request President Obama provides clemency to Edward Snowden
Featured image via How To Use Linux


![A classic film is given new life in a ground-breaking, serial Twitter drama [VIDEO]](https://www.thecanary.co/wp-content/uploads/2016/10/Flowers-for-Algernon.jpg)